Firewall router
Network segmentation/isolating
The requirements for IT security are continually increasing in industry. Yet at the same time we often see a lack of personnel resources for implementing this security. The IT security products from W&T are designed for straightforward implementation of concrete security requirements. As a basic measure for many IT security concepts the W&T micro-firewalls isolate critical systems (older devices, IoT systems, etc.) on a secure island in your network. The Microwall Bridge provides security when needed, quickly and simply, while the Microwall VPN and IO provide additional protection.
Segmenting in just a few minutes - here’s how it’s done:
You activate the video function using the following button, whereby you use the provider Google and (at your own risk in terms of data protection ;) share data with it.
- Starting up Microwall
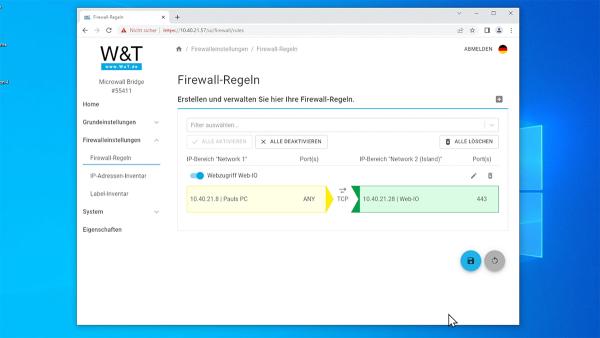
- Setting up firewall rules
- Swap network cable of the device to be secured...
- ...done!
Firewall router with VPN
The Microwall VPN as a firewall router enables secure access to maintenance islands in the customer network, builds VPN tunnels between two network locations, and expands your secure islands by adding cryptographically authenticated access possibilities. Discover mode supports you in the secure and controlled commissioning of new, unknown island hosts and provides a detailed overview of the connection attempts.
The Microwall IO includes all the functions of the Microwall VPN. Use the digital in- and outputs to switch remote maintenance and firewall-specific actions in automatoin and process environments. Using a PLC output, a simple button or switch etc. VPN access, certain firewall rules or the status of the network interfaces can be controlled.
Firewall bridge without modifying the IP setup
The Microwall Bridge segments sensitive network areas without changing the IP configuration of the components which have been isolated. The preferred area of application is therefore the easiest possible, add-on security expansion of existing infrastructures.


